Someone just walked away with $25 million in ETH after exploiting Resolv’s USR stablecoin by minting 80 million tokens from a $200,000 USDC deposit. Single wallet controlled minting permissions, no multisig, insufficient auditing. The attacker dumped everything across Curve in 17 minutes, crashing USR from $1 to $0.025.
The standard response focuses on operational security failures. Single key instead of multisig, inadequate auditing, poor access controls. All true. But there’s a deeper architectural point about how intent-based systems prevent this class of exploit.
The exploit worked because the minting contract allowed direct execution of privileged functions through normal transaction calls. Wallet had the key, submitted transactions to mint unlimited tokens, transactions executed. Security relied entirely on that key staying secure and access control logic being correct. When either assumption broke, system failed catastrophically.
Intent-based protocols like Anoma handle privileged operations differently through validity predicates that encode constraints as verifiable logic. When you want to execute a privileged operation, you express the desired outcome as an intent. Validity predicates verify that intent satisfies all constraints before execution proceeds.
For stablecoin minting, validity predicates could enforce that minting requires corresponding collateral deposit, that minting ratio cannot exceed defined parameters, that large mints require multiple authorizations. These constraints get verified cryptographically as part of intent settlement rather than being checked through access control that can be bypassed if keys are compromised.
The architectural difference: transaction-based systems rely on access control to prevent unauthorized actions. If you have the right key you can execute any function, regardless of whether execution makes sense given system state. Intent-based systems rely on validity predicates that must be satisfied regardless of who submits the intent.
Imagine Resolv minting implemented with intent architecture. Attacker expresses intent to mint 50 million USR. Validity predicates check whether corresponding collateral exists to back that minting at defined ratio. Check fails because $200,000 USDC does not back 50 million tokens. Intent gets rejected before execution. Even with the authorized key, the intent cannot execute because it violates validity predicates encoding system constraints.
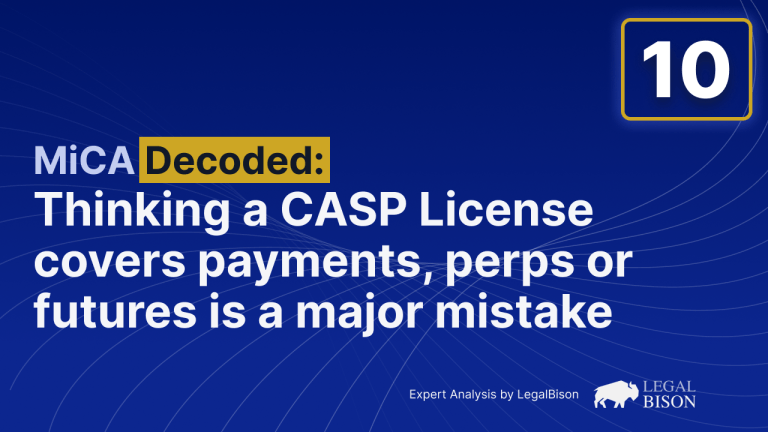
CowSwap is different. It uses intent architecture for order settlement and MEV protection through solver competition and batch auctions, not for access control on privileged functions. CowSwap prevents MEV extraction but is not designed to prevent exploits where privileged functions execute in ways that violate system constraints.
The Resolv case specifically would have benefited from validity predicates enforcing collateralization ratios, minting limits, and constraints that should hold regardless of who executes the function. Even with compromised keys, intents to mint unbacked tokens would get rejected by validity predicates before execution.
This is not claiming intent architecture prevents all exploits. Validity predicates can be implemented incorrectly just like access control. But encoding constraints as validity predicates that must be satisfied provides meaningful additional security for privileged operations beyond just checking whether the caller is authorized.
Anoma’s architecture with validity predicates and atomic intent settlement is designed specifically to address these problems. Whether it would have prevented this specific exploit depends on implementation details, but the architectural approach of encoding constraints as verifiable logic rather than relying solely on access control provides different security properties worth considering.
Curious whether others building DeFi protocols are thinking about intent architecture as security improvement or whether focus remains primarily on traditional access control and multisig approaches.
[link] [comments]

You can get bonuses upto $100 FREE BONUS when you:
💰 Install these recommended apps:
💲 SocialGood - 100% Crypto Back on Everyday Shopping
💲 xPortal - The DeFi For The Next Billion
💲 CryptoTab Browser - Lightweight, fast, and ready to mine!
💰 Register on these recommended exchanges:
🟡 Binance🟡 Bitfinex🟡 Bitmart🟡 Bittrex🟡 Bitget
🟡 CoinEx🟡 Crypto.com🟡 Gate.io🟡 Huobi🟡 Kucoin.












Comments